Organization-level Environment Variables and Secrets in GitHub Actions
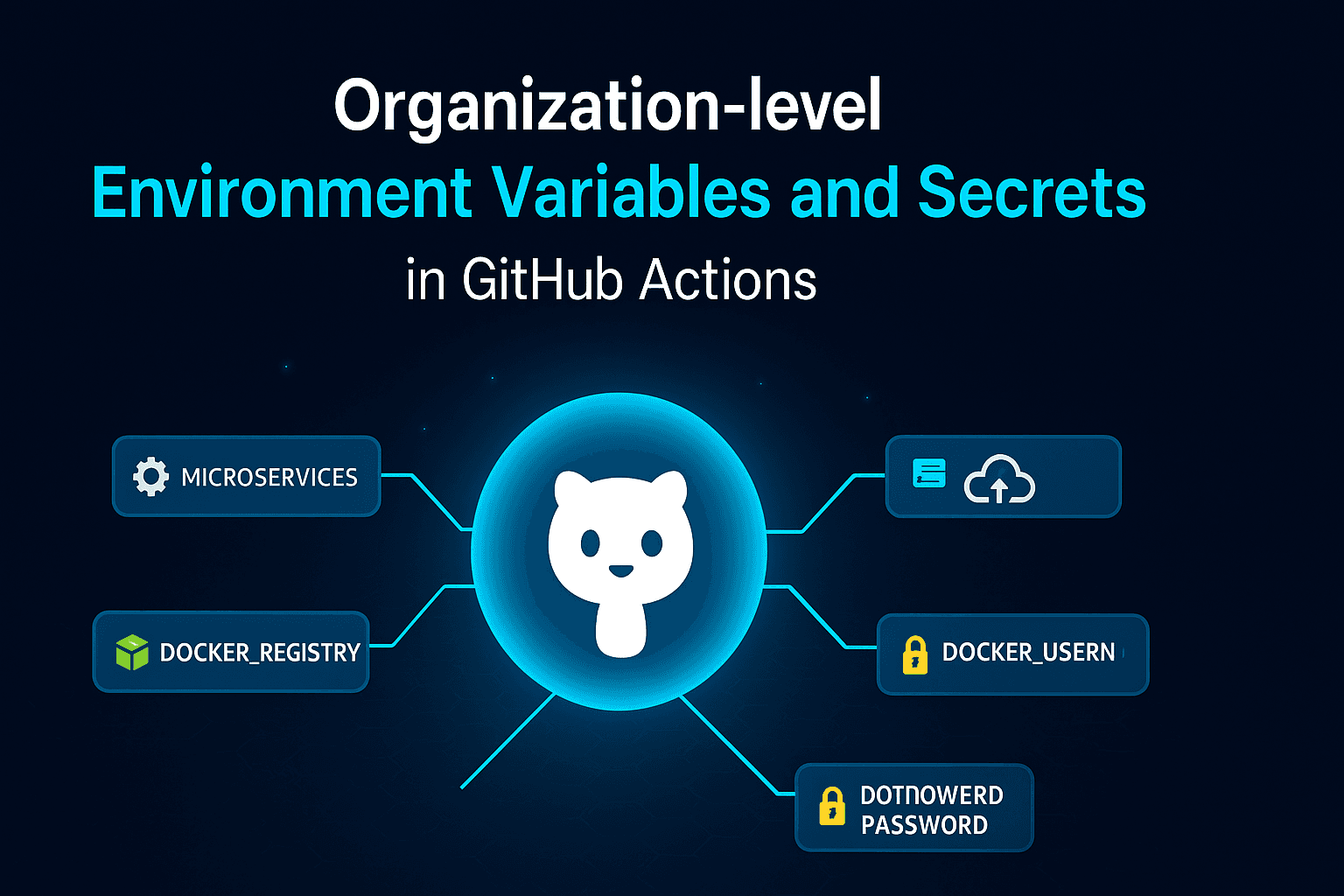
When teams scale, managing workflows across multiple repositories becomes more complex. Each project often shares common configuration values, cloud credentials, or deployment secrets. Instead of duplicating these across repositories, GitHub provides a centralized solution: organization-level environment variables and secrets.
In this article, we’ll explore how they work, when to use them, and how to integrate them into your CI/CD pipelines.
Why Organization-level Variables and Secrets?
Repository-level variables and secrets are useful, but they only apply to a single repository. If you manage multiple repositories within the same organization (for example, microservices architecture), repeating the same values across repositories is inefficient and error-prone.
Organization-level variables and secrets allow you to:
Define once and use in all repositories within the organization.
Standardize configurations across projects.
Reduce maintenance overhead.
Strengthen security by managing credentials in a single place.
Types of Organization-level Data
Organization Variables
Non-sensitive values such as
DOCKER_REGISTRY_URL,NODE_VERSION, orDEPLOY_REGION.Available in all workflows in repositories under the organization.
Accessed using
${{ vars.VAR_NAME }}.
Organization Secrets
Encrypted, hidden values like API keys, service account credentials, and cloud tokens.
Available to all repositories in the organization, unless access is restricted.
Accessed using
${{ secrets.SECRET_NAME }}.
How to Set Them
Go to your GitHub organization’s page.
Navigate to: Settings → Secrets and variables → Actions.
You’ll see two tabs:
Variables → for plain-text values.
Secrets → for sensitive data.
Choose whether they should apply to all repositories or to a selected set of repositories.
Example Use Case: Multi-service Deployment with Docker
Imagine an organization managing multiple microservices, each in its own repository. They all deploy Docker images to the same registry. Instead of configuring credentials in every repo, you can define them once at the organization level.
Organization Variables:
DOCKER_REGISTRY =ghcr.io/my-orgDEPLOY_ENV = production
Organization Secrets:
DOCKER_USERNAMEDOCKER_PASSWORD
Workflow Example:
name: Build and Push Docker
on: [push]
jobs:
docker:
runs-on: ubuntu-latest
steps:
- name: Checkout repository
uses: actions/checkout@v3
- name: Log in to Docker registry
run: echo "${{ secrets.DOCKER_PASSWORD }}" | docker login ${{ vars.DOCKER_REGISTRY }} -u ${{ secrets.DOCKER_USERNAME }} --password-stdin
- name: Build Docker image
run: docker build -t ${{ vars.DOCKER_REGISTRY }}/myservice:${{ github.sha }} .
- name: Push Docker image
run: docker push ${{ vars.DOCKER_REGISTRY }}/myservice:${{ github.sha }}
What’s happening here?
Organization-level variable
${{ vars.DOCKER_REGISTRY }}ensures all repositories use the same registry.Secrets
${{ secrets.DOCKER_USERNAME }}and${{ secrets.DOCKER_PASSWORD }}handle authentication securely.Any new repository added to the org can reuse this configuration instantly.
Benefits of Organization-level Variables and Secrets
Centralized Management: Define once, use everywhere.
Security: Sensitive data is encrypted and scoped properly.
Consistency: Prevents mismatches across repositories.
Scalability: Ideal for organizations with dozens of repositories.
Key Takeaways
Use organization variables for non-sensitive shared values.
Use organization secrets for sensitive credentials shared across repositories.
Control which repositories have access for tighter security.
Great for scaling CI/CD pipelines across multiple projects.
Conclusion
Organization-level environment variables and secrets simplify configuration management at scale. By centralizing values and credentials, you can eliminate redundancy, reduce risk, and improve maintainability across all repositories.
If your team is managing multiple repositories under one organization, adopting organization-level variables and secrets is a best practice for efficiency and security.